Manual payroll processing is one of the biggest sources of errors, delays, and compliance issues in Indian businesses.Risks of Manual PayrollIncorrect salary calculationsMissed statutory deductionsCompliance penaltiesEmployee dissatisfactionBenefits of Payroll AutomationAccurate salary computationAutomated PF...
Read MoreTraditional biometric systems are expensive, hardware-dependent, and difficult to manage. Face recognition using mobile apps is rapidly becoming the preferred alternative.Why Face-Based Attendance is GrowingNo hardware installation requiredWorks remotely and on-siteReduces proxy attendanceFaster clock-in and ...
Read MoreManaging field employees is one of the biggest challenges for businesses in sales, logistics, and services. Without visibility, productivity drops and accountability suffers.Common Challenges with Field StaffFake or incorrect attendanceNo visibility on daily routesDifficulty measuring actual work hoursDelayed...
Read MoreManaging HR operations manually is no longer sustainable for growing businesses. From attendance tracking to payroll compliance, SMEs in India need a modern HRMS that is simple, affordable, and scalable.Why SMEs Need an HRMS TodayManual attendance leads to errors and disputesPayroll compliance is getting stri...
Read MoreIntegrating payroll with employee benefits management helps companies to streamline operations and improve employee satisfaction. By connecting these two elements, businesses can save time, reduce errors, and create a better experience for their employees. In this blog, we’ll discuss the benefits of int...
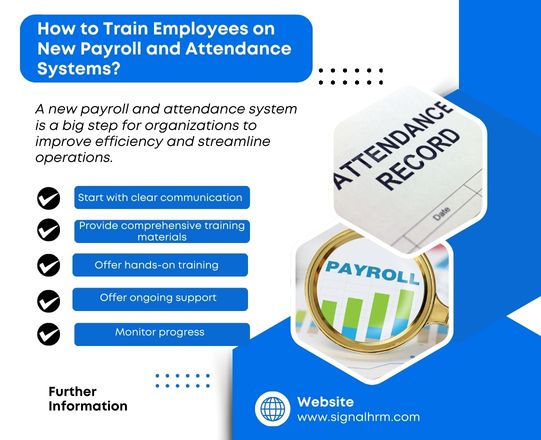
Read MoreIntroducing a new payroll and attendance system is a big step for organizations to improve efficiency and streamline operations. However, it can also be overwhelming for employees who are used to the old system. Therefore, organizations must conduct proper training to ensure smooth adoption, reduce errors...
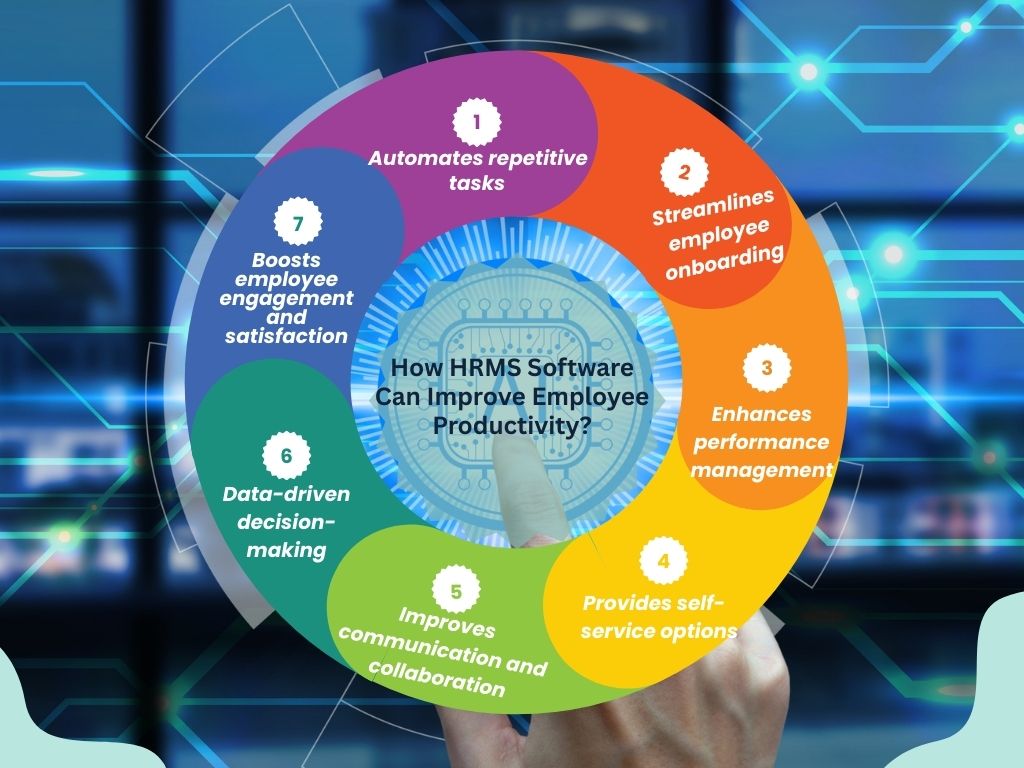
Read MoreBusinesses need to streamline processes to maximize efficiency and productivity of employees. Human resource management system (HRMS) helps them to manage HR functions seamlessly. By automating administrative tasks and improving communication, HRMS helps employees to focus on their core responsibilities r...
Read MoreThe Role of AI in Modern Payroll SystemsOrganizations are increasingly using artificial intelligence (AI) to automate and optimize their payroll processes. AI-powered payroll software helps organizations to reduce manual errors, ensure compliance, and streamline payroll operations efficiently. According ...
Read MoreOrganizations need to ensure the safety of sensitive employee information in this digital world. Therefore, payroll management software must have the functionalities to protect confidential data such as employee salaries, tax information, and bank account numbers. Let’s find out why data security should...
Read MoreOrganizations have their predefined protocols and standards to manage human resources, accomplish goals, and achieve desired targets. Varying needs and requirements lead to the demand for different types of HRMS solutions. This has led to increased demand for custom HRMS software that accommodates specific ne...
Read More